In today’s digital landscape, email remains a cornerstone of both personal and professional communication. However, this reliance on electronic correspondence has opened the door to various cyber threats, notably spam and phishing attacks. While these terms are often used interchangeably, they represent distinct challenges with unique characteristics and implications. Understanding the differences between spam and phishing is crucial for safeguarding sensitive information and maintaining cyber security.
Defining Spam
Spam refers to unsolicited messages sent in bulk, typically for commercial purposes. These messages often clutter inboxes with irrelevant or promotional content, ranging from advertisements for products and services to dubious offers and schemes. The primary intent behind spam is to promote or sell, rather than to cause direct harm to the recipient.
Characteristics of Spam Emails
Unsolicited Nature: Spam emails are sent without the recipient’s consent, often to a large number of addresses obtained through various means.
Promotional Content: They usually contain advertisements or promotions for products, services, or events.
Generic Messaging: Spam messages often lack personalisation and are designed to appeal to a broad audience.
Low Threat Level: While annoying, most spam emails are not inherently malicious. However, some may contain links to malicious websites or attachments that can install malware.
Evolution of Spam
In the early days of the internet, email spam was primarily a nuisance, filling up inboxes with unwanted advertisements and irrelevant or promotional comments. Over time, the volume of spam grew exponentially, leading to the development of spam filters and regulations aimed at curbing its spread. Legislative measures, such as the CAN-SPAM Act in the United States, have been implemented to set guidelines for commercial emails and provide recipients with options to opt out of future messages. Despite these efforts, spam continues to evolve, with spammers now targeting social media platforms through irrelevant or promotional comments, making it even more important to stay vigilant against these persistent threats.

Defining Phishing
Phishing is a more insidious threat, involving fraudulent communications designed to deceive individuals into divulging sensitive information or performing actions compromising their security. Phishing attacks often masquerade as legitimate communications from trusted entities, such as banks, government agencies, or well-known companies.
Characteristics of Phishing Emails
Deceptive Appearance: Phishing emails are crafted to closely resemble legitimate communications, often using official logos, language, and formatting.
Sense of Urgency: They frequently employ urgent or threatening language to prompt immediate action from the recipient.
Requests for Sensitive Information: Phishing messages often ask for personal data, such as login credentials, financial information, or Social Security numbers.
Malicious Links or Attachments: They may contain links to fake websites designed to harvest information or attachments that install malware upon opening.
Types of Phishing Attacks
Spear Phishing: Targeted attacks aimed at specific individuals or organisations, often personalised using information gathered from social media or other sources.
Whaling: A form of spear phishing that targets high-profile individuals, such as executives or public figures, with the intent of stealing sensitive data or funds.
Clone Phishing: Involves creating a nearly identical copy of a legitimate email that the victim has previously received, replacing legitimate links or attachments with malicious ones.
Smishing and Vishing: Phishing attempts conducted via SMS messages (smishing) or voice calls (vishing), aiming to trick individuals into revealing personal information.
Recognising Phishing Attempts
To protect against phishing scams, it’s essential to recognise common warning signs:
Mismatched URLs: Hovering over a link reveals a different URL than the one displayed.
Generic Greetings: Lack of personalisation, such as addressing the recipient as “Dear Customer.”
Suspicious Attachments: Unexpected attachments, especially those prompting immediate opening.
Unusual Sender Address: Email addresses that don’t match the purported sender’s domain.
Implications of Spam and Phishing
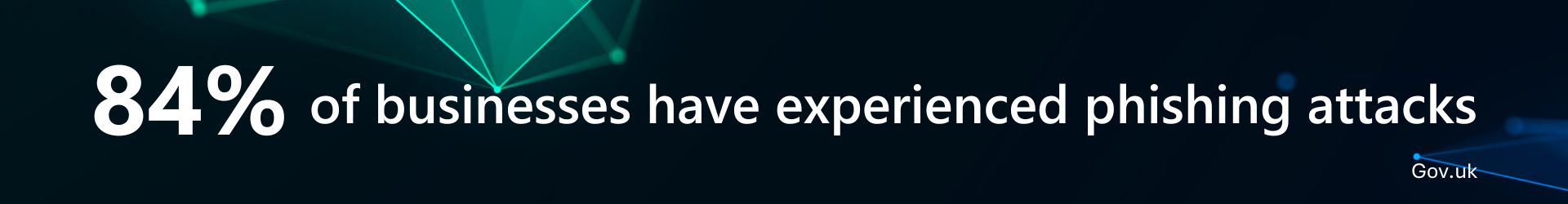
While both spam and phishing can be disruptive, phishing poses a more significant threat due to its potential to cause substantial harm:
Data Breaches: Successful phishing attacks can lead to unauthorised access to sensitive data, resulting in data breaches.
Financial Loss: Victims may suffer financial losses through fraudulent transactions or identity theft.
Reputational Damage: Organisations compromised by phishing attacks may experience loss of trust and credibility.
Preventative Measures
To safeguard against spam and phishing attacks, individuals and organisations can implement several strategies:
Utilise Spam Filters: Employ email filters to detect and block unsolicited messages.
Educate and Train: Conduct regular cyber security training to help individuals recognise and respond to phishing attempts.
Verify Requests: Always verify unsolicited requests for sensitive information through official channels before responding.
Keep Software Updated: Regularly update software and security protocols to protect against known vulnerabilities.
Use Multi-Factor Authentication (MFA): Implement MFA to add an extra layer of security to accounts.
Report Suspicious Communications: Encourage reporting of suspicious emails or messages to the appropriate authorities or IT departments.
Conclusion
In the ongoing battle of spam vs phishing, understanding the risks associated with each is crucial for maintaining cyber security. While spam emails and social media spam clutter inboxes and social media platforms with unwanted messages, phishing attacks are far more dangerous, aiming to steal sensitive information or install malware. By implementing strong security measures, using spam filters, and educating employees on recognising phishing attempts, businesses can significantly reduce their exposure to cyber threats.
We offer advanced email security, phishing awareness training, and continuous threat monitoring to help protect your organisation. Get in touch with our team today to strengthen your defences against spam and phishing attacks.
Frequently Asked Questions
Are phishing scams limited to emails?
No, phishing scams also occur via sms messages (phishing spam), phone calls (vishing), and social media platforms through social media spam or fake profiles. Cyber criminals exploit multiple channels to trick victims into sharing sensitive information.
Can spam emails be dangerous?
Yes, while most email spam is simply annoying, some spam emails may contain malicious links, lead to malicious websites, or attempt to trick recipients into revealing personal information. It’s essential to use spam filters and avoid clicking on suspicious emails.
What is the main difference between spam and phishing?
Spam refers to unsolicited emails, often containing advertisements or irrelevant or promotional comments that clutter inboxes. Phishing, on the other hand, is a malicious attempt to deceive recipients into providing sensitive information, such as login credentials or financial details, often by impersonating a legitimate source.
What should I do if I receive a phishing email?
If you suspect a phishing attempt, do not click on any links or download attachments. Instead:
- Report suspicious emails to your IT team or email provider.
- Forward phishing emails to relevant cyber security authorities.
- Verify the sender by visiting the official website directly.
- Educate colleagues or employees about phishing tactics to prevent future attacks.
